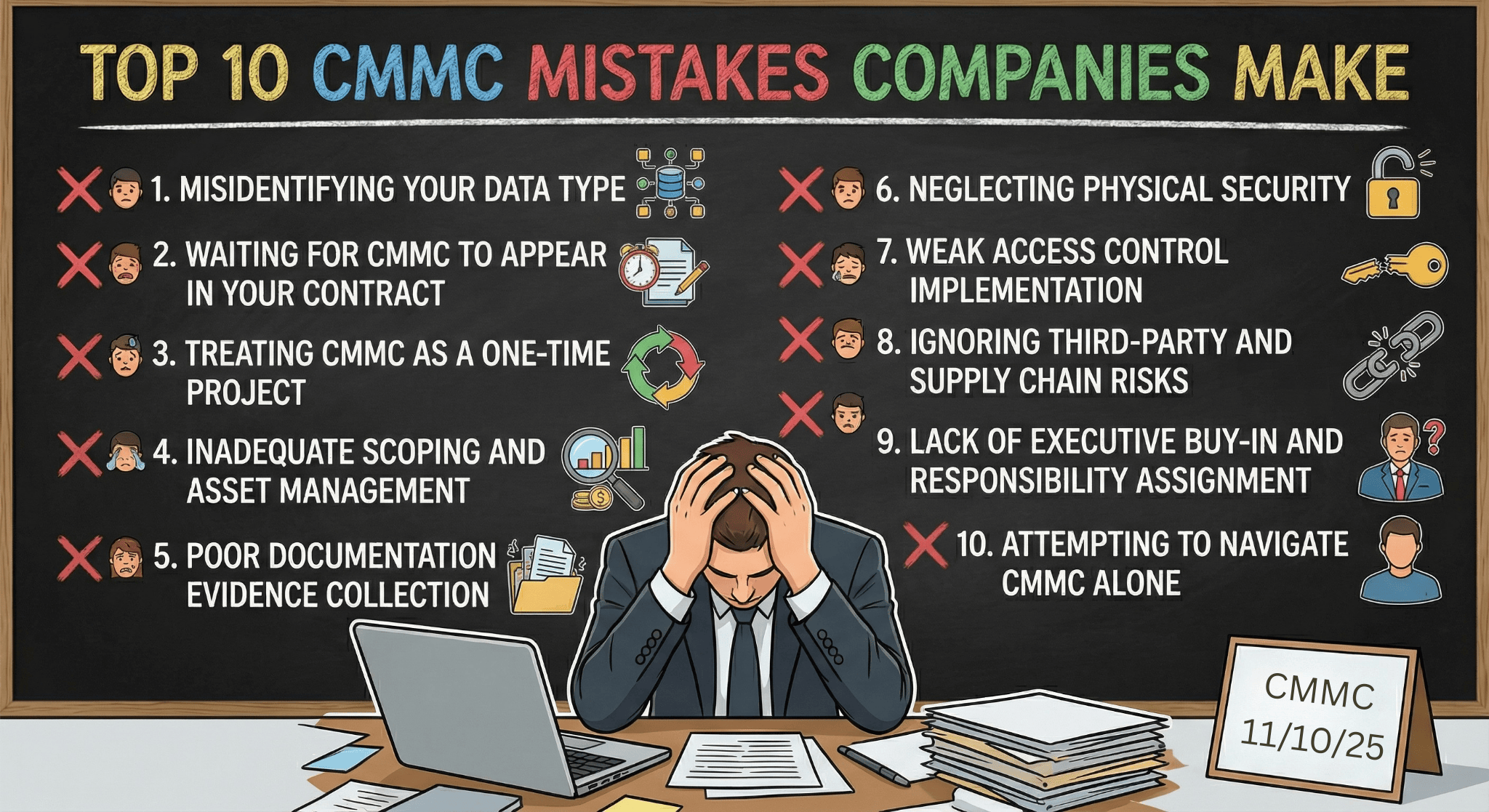
The Top 10 Mistakes Companies Make with CMMC
The Cybersecurity Maturity Model Certification (CMMC) has become a critical requirement for defense contractors looking to secure or maintain contracts with the Department of Defense. Despite its importance, many contractors stumble on common missteps that delay certification, increase costs, or even risk contract eligibility. Avoiding these mistakes can save time, money, and frustration.
Here are the top 10 mistakes contractors make with CMMC and how you can sidestep them.
1. Misidentifying Your Data Type
One of the most widespread errors is confusing Federal Contract Information (FCI) with Controlled Unclassified Information (CUI). This misstep leads to wrong scoping and applying incorrect CMMC levels, either over-implementing controls unnecessarily or leaving gaps that cause non-compliance. Always carefully classify your data by reviewing contracts and referencing official CUI registries.
2. Waiting for CMMC to Appear in Your Contract
Many companies delay preparation until CMMC clauses show up in their current contracts. This reactive approach leaves little time to build out the necessary controls, document processes, or train staff. Proactive preparation is key, start building your cybersecurity foundation now so you aren’t rushed later.
3. Treating CMMC as a One-Time Project
Completing your System Security Plan (SSP) and controls checklist once and then setting it aside is a costly mistake. Systems, personnel, and processes evolve, which means your cybersecurity program needs constant maintenance and revision. Treat CMMC compliance as an ongoing operational requirement, with regular updates and assessments.
4. Inadequate Scoping and Asset Management
Failing to properly scope your CUI environment and asset boundaries can lead to overlooking critical systems or overextending security efforts. Conduct thorough data flow mapping and maintain an accurate, current inventory of all assets that handle sensitive information.
5. Poor Documentation and Evidence Collection
Strong technical controls aren’t enough. Assessors expect to see well-maintained policies, procedures, and evidence that controls are implemented and effective. Don’t wait until right before your assessment to gather documentation… make continuous record-keeping part of your process.
6. Neglecting Physical Security
CMMC includes physical security requirements, but contractors often focus only on digital protections. Facilities, server rooms, visitor logs, and secure hardware disposal processes must be addressed to avoid findings.
7. Weak Access Control Implementation
This will haunt you. Nothing worse than going through your assessment just to be stopped because you fail these controls. Improper access management, like overly permissive user rights or failing to implement least privilege principles, leaves your environment exposed. Develop clear access policies, review access regularly, and promptly remove rights when employees change roles or leave.
8. Ignoring Third-Party and Supply Chain Risks
Your compliance depends not only on your own controls but also on your suppliers’ security practices. Prime contractors must ensure that subcontractors meet required CMMC levels. Failure to incorporate supply chain security can jeopardize your entire compliance effort.
9. Lack of Executive Buy-in and Responsibility Assignment
Without clear leadership support and defined accountability, CMMC initiatives stall. Executive sponsorship ensures resources and attention stay focused on compliance. Assign specific roles and responsibilities to team members to maintain momentum and clarity.
10. Attempting to Navigate CMMC Alone
The complexity of CMMC 2.0 means that many organizations benefit from outside expertise. Trying to “go it alone” often results in costly mistakes or delays. Engaging trusted third-party consultants or advisors can help you avoid pitfalls, streamline certification, and ensure you meet all requirements.
Avoiding these common mistakes sets you on a smoother path to CMMC certification and helps protect your ability to compete for and win DoD contracts. If you want, assistance can be provided to build a detailed readiness plan or provide templates and tools to manage your compliance journey successfully.